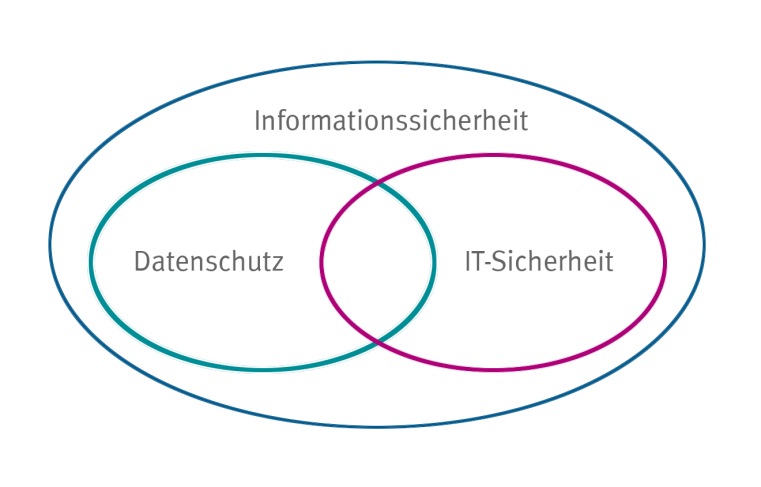
INFORMATION SECURITY, IT-SECURITY AND DATA PROTECTION
Information security incorporates all types of information, including those on paper (analog) or in people's heads. IT security is only one part of information security and covers only information processed with information technology (IT). Data protection, on the other hand, exclusively covers the protection of personal data, regardless of how it is processed. All three areas - information security, IT security, data protection - have many intersections and correspondingly overlapping threat scenarios and protection measures.